Endpoint protection software has become a cornerstone of modern cybersecurity, providing essential safeguards against an increasingly complex threat landscape. With the rise of remote work and the proliferation of devices accessing corporate networks, ensuring that every endpoint is secure is more important than ever. This software not only protects individual devices but also helps in maintaining the integrity of entire organizational networks.
In this exploration, we’ll dive into the various types of endpoint protection solutions available, highlight key features that businesses should prioritize, and discuss the innovative technologies shaping the future of endpoint security. As we unravel these layers, it becomes clear that investing in robust endpoint protection is not just a technical necessity but a strategic business imperative.
Overview of Endpoint Protection Software
In an increasingly digital landscape, endpoint protection software plays a crucial role in safeguarding organizational data and devices. This software is designed to prevent, detect, and respond to threats targeting endpoints such as computers, mobile devices, and servers. With the rise of remote work and mobile operations, the importance of endpoint protection cannot be overstated.Endpoint protection solutions come in various forms, tailored to different business needs.
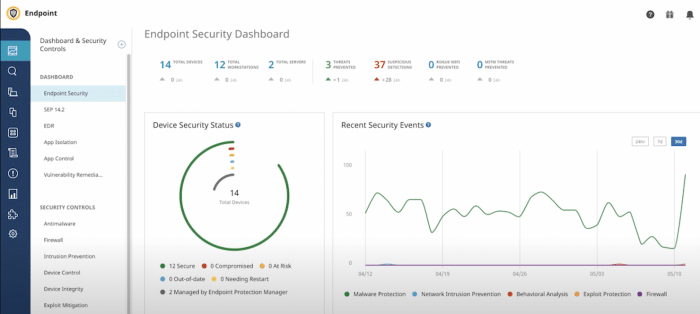
The primary types include antivirus, anti-malware, endpoint detection and response (EDR), and unified endpoint management (UEM). Each type offers unique features and capabilities, allowing businesses to choose the solution that best fits their security requirements.When selecting endpoint protection software, businesses should focus on several key features:
- Real-time threat detection and response capabilities.
- Comprehensive reporting and analytics tools.
- Integration with existing security infrastructure.
- Scalability to accommodate future growth.
- User-friendly interface for ease of management.
Business Innovation in Endpoint Security
Innovative technologies are continuously shaping the landscape of endpoint protection. Artificial intelligence (AI) and machine learning are at the forefront, providing advanced threat detection and response capabilities. These technologies help in analyzing vast amounts of data to identify patterns and anomalies that signify a potential threat.Over the years, endpoint protection software has significantly evolved from basic antivirus solutions to sophisticated systems capable of responding to advanced persistent threats.
For instance, early antivirus programs mainly focused on signature-based detection, while modern solutions leverage behavioral analysis and machine learning for real-time threat identification.Endpoint protection plays a vital role in facilitating business innovation by ensuring a secure environment for digital transformation. With robust endpoint security in place, organizations can confidently adopt new technologies and methodologies, enhancing their overall operational efficiency.
International Business and Cybersecurity
Global regulations significantly impact the deployment of endpoint protection software for international businesses. Compliance with standards such as GDPR in Europe or HIPAA in the United States necessitates stringent data protection measures, affecting how endpoint protection is implemented across various jurisdictions.To effectively implement endpoint protection in multinational corporations, businesses must adopt a standardized approach that addresses local regulations while maintaining overall corporate security policies.
This includes establishing centralized management systems that can adapt to local compliance requirements.International businesses face several challenges in endpoint security management, including differing regulations, diverse threat landscapes, and varying levels of cybersecurity maturity across regions. Addressing these challenges requires a cohesive strategy that aligns security practices with the organization’s global objectives.
Business Management Perspectives
Managing endpoint protection is essential for organizations to maintain a strong security posture. An effective endpoint security strategy not only safeguards sensitive data but also contributes to overall business management efficiency by minimizing downtime and loss due to cyber incidents.Effective endpoint security contributes to business management efficiency through streamlined operations, reduced security incidents, and enhanced employee productivity. When employees feel secure in their digital environment, they can focus on their core responsibilities without the distraction of potential cyber threats.Best practices for managing endpoint protection policies in a business setting include:
- Regularly updating and patching software to close vulnerabilities.
- Conducting employee training sessions on security awareness.
- Implementing multi-factor authentication for sensitive systems.
- Continuously monitoring endpoints for suspicious activity.
Marketing Direct for Endpoint Protection Solutions
Creating effective marketing strategies for promoting endpoint protection software is vital for reaching potential customers. Identifying the right channels and messaging can significantly enhance market penetration and customer engagement.The target audience for endpoint protection solutions spans various industries, including finance, healthcare, and manufacturing. Each segment has unique security needs, making it essential to tailor marketing efforts accordingly. For instance, healthcare organizations may prioritize compliance and patient data protection, while financial institutions may focus on fraud prevention.Case studies play a crucial role in enhancing the marketing of endpoint protection software.
By showcasing real-world examples of successful implementations, businesses can provide tangible evidence of the software’s effectiveness and build trust with prospective clients.
Business Networking in Cybersecurity
Building a professional network focused on cybersecurity and endpoint protection can yield significant benefits for businesses. Networking facilitates knowledge sharing, collaboration on security initiatives, and access to new technologies and solutions.The benefits of networking with other businesses include the exchange of best practices, insights into emerging threats, and opportunities for joint ventures in cybersecurity advancements. Engaging with peers in the industry encourages a proactive approach to security challenges.Successful collaborations in the field of cybersecurity often result in enhanced protection and innovation.
For example, partnerships between software vendors and cybersecurity firms can lead to the development of cutting-edge solutions that address evolving threats.
Business Outsourcing of Cybersecurity Services
Outsourcing endpoint protection services offers several advantages for businesses looking to optimize their cybersecurity efforts. By leveraging external expertise, organizations can benefit from advanced technologies and skilled professionals without the overhead of maintaining an in-house team.However, outsourcing cybersecurity functions does carry potential risks, such as loss of control over security protocols and data privacy concerns. Businesses must carefully evaluate service providers and ensure they align with their security objectives and compliance requirements.Choosing the right service provider for endpoint protection involves assessing their track record, expertise, and understanding of the specific security landscape relevant to the business’s industry.
A thorough vetting process is essential to ensure a successful partnership.
Workplace Safety and Endpoint Protection
There is a significant relationship between endpoint protection and workplace safety. A secure digital environment ensures that employees can work effectively without the fear of data breaches or cyberattacks that could disrupt operations.To ensure employees follow best practices for endpoint security, organizations should provide clear guidelines and regular training sessions. Emphasizing the importance of strong passwords, recognizing phishing attempts, and securing personal devices can significantly enhance workplace safety.Inadequate endpoint protection can lead to severe consequences, including data breaches, financial losses, and damage to the organization’s reputation.
Therefore, investing in robust endpoint security measures is crucial for maintaining a safe working environment.
Risk Management Strategies
Implementing risk assessment procedures is vital for identifying vulnerabilities in endpoint devices. Regular assessments help organizations understand their security posture and prioritize areas that require immediate attention.Endpoint protection software plays a key role in mitigating risks by providing comprehensive coverage against various types of cyber threats. By employing advanced detection methods and response capabilities, organizations can significantly reduce the likelihood of successful attacks.Integrating endpoint protection into a broader risk management framework involves aligning security measures with overall business objectives and ensuring that all employees are aware of their responsibilities in maintaining security standards.
Sales Management and Endpoint Solutions
Identifying effective sales strategies specific to the endpoint protection software market is essential for driving revenue growth. Understanding customer needs and aligning solutions with their unique challenges can significantly enhance sales success.Sales teams should be trained on the intricacies of endpoint protection solutions to effectively communicate their benefits to potential customers. This includes understanding key features, compliance requirements, and the overall value proposition of the software.Providing ongoing training and resources for sales teams ensures they remain knowledgeable about the latest trends and developments in endpoint protection, enhancing their ability to engage with prospects effectively.
Business Security Trends
Current trends shaping the future of endpoint protection software include the growing integration of AI, an increase in remote work, and a focus on zero-trust security models. These trends are reshaping how organizations approach endpoint security, driving innovation and adaptation.Cybersecurity awareness training is becoming increasingly important for enhancing endpoint security. Educating employees about potential threats and promoting best practices can significantly reduce the risk of human error, which is often a leading cause of security breaches.Emerging threats, such as ransomware and sophisticated phishing attacks, require endpoint protection software to evolve continuously.
Organizations must stay informed about these threats and adapt their security measures accordingly to maintain robust protection.
Strategic Planning for Cybersecurity
Developing strategic plans that incorporate endpoint protection considerations is essential for organizations looking to bolster their cybersecurity posture. Strategic planning should align with overall business goals and focus on effectively managing risks associated with endpoint vulnerabilities.Businesses can utilize templates to create effective endpoint protection strategies, outlining key objectives, resource requirements, and implementation timelines. A well-defined strategy provides clarity and direction for security initiatives.Identifying key performance indicators (KPIs) for measuring endpoint protection effectiveness allows organizations to evaluate the success of their security measures.
Regular reviews of these metrics enable continuous improvement and adaptation to the changing threat landscape.
Team Building for Cybersecurity Awareness
Team collaboration is crucial for enhancing endpoint protection practices within an organization. Fostering a culture of security awareness encourages employees to take ownership of their roles in maintaining a secure environment.Engaging in team-building activities focused on cybersecurity training can enhance knowledge and collaboration among employees. These activities promote a shared understanding of security policies and encourage proactive behavior.Creating a culture of security awareness within teams involves consistent communication, recognition of good practices, and ongoing training.
This culture not only strengthens endpoint security but also contributes to a more resilient organization.
Workplace Communication on Cybersecurity Policies
Effectively communicating endpoint protection policies to employees is essential for ensuring compliance and fostering a culture of security. Clear communication helps employees understand their responsibilities and the importance of adhering to security protocols.Organizations should establish guidelines for regular updates and training sessions on endpoint security measures. Keeping employees informed about new threats and security practices strengthens the overall security posture.The impact of clear communication on adherence to cybersecurity protocols cannot be understated.
When employees understand the rationale behind security policies, they are more likely to comply and contribute to a secure workplace environment.
Closing Notes
In summary, the landscape of endpoint protection software is dynamic, shaped by technological innovations and the evolving needs of businesses. As organizations continue to navigate the complexities of cybersecurity, the importance of effective endpoint protection cannot be overstated. By implementing the right solutions and fostering a culture of security awareness, businesses can not only protect their assets but also enhance their operational efficiency and drive innovation forward.
Question Bank
What is endpoint protection software?
Endpoint protection software is a security solution that protects endpoint devices like computers, mobile devices, and servers from cyber threats.
Why is endpoint protection important for businesses?
It is vital as it helps prevent data breaches, malware infections, and other security incidents that can jeopardize business operations and sensitive information.
How does endpoint protection software evolve?
It evolves by incorporating advanced technologies such as artificial intelligence and machine learning to better detect and respond to emerging threats.
Can small businesses benefit from endpoint protection?
Absolutely! Small businesses can greatly benefit from endpoint protection as they are often targeted by cyber attackers due to limited security measures.
What are some best practices for managing endpoint protection?
Best practices include regular software updates, employee training on cybersecurity, and implementing a comprehensive security policy.





![41 SMS Marketing Statistics, Trends, and Insights [Updated for 2024]](https://agadoio.info/wp-content/uploads/2025/07/sms-marketing-statistics-1024x512-1-300x150.jpg)